A Cybersecurity Specialist for a defense company safeguards critical military systems and sensitive information from cyber threats by implementing advanced security protocols and monitoring network activities. They conduct vulnerability assessments and respond to cyber incidents to ensure the integrity and confidentiality of defense operations. Their expertise supports the continuous protection of national security assets against evolving cyber attacks.
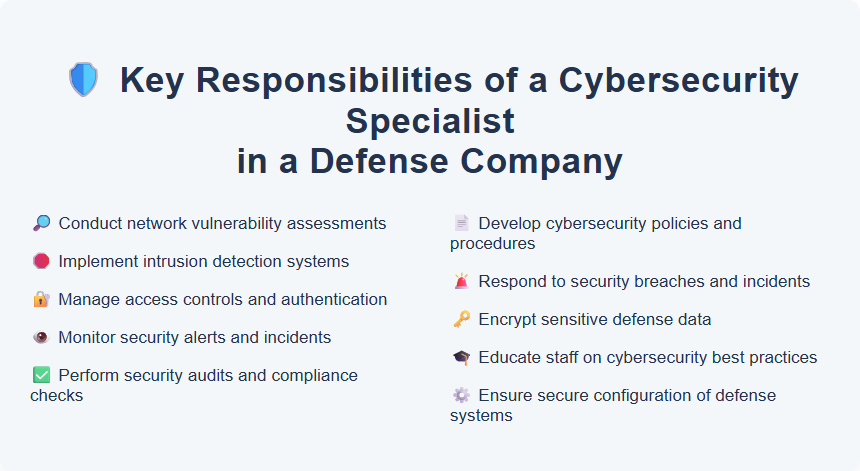
Conduct network vulnerability assessments
Perform thorough network vulnerability assessments to identify potential security weaknesses and risks within IT infrastructures. Utilize advanced tools and techniques to analyze network configurations, detect vulnerabilities, and recommend actionable remediation strategies. Collaborate with cybersecurity teams to implement improvements and ensure robust protection against emerging threats.
Implement intrusion detection systems
Design, deploy, and maintain intrusion detection systems to monitor network traffic for suspicious activity and potential security breaches. Analyze alerts, create detailed reports, and collaborate with IT teams to enhance system defenses and minimize vulnerabilities. Continuously update detection signatures and system configurations to adapt to evolving cyber threats and ensure robust organizational security.
Manage access controls and authentication
Ensure robust management of access controls and authentication by implementing role-based permissions, multi-factor authentication (MFA), and continuous monitoring to prevent unauthorized access. Regularly update and audit user access rights to maintain security compliance and reduce risk exposure. Utilize advanced authentication protocols and tools to enhance system integrity and protect sensitive data.
Monitor security alerts and incidents
Monitor security alerts and incidents by analyzing real-time data from intrusion detection systems and security information event management (SIEM) tools. Investigate potential threats and coordinate with IT teams to implement prompt mitigation strategies, ensuring compliance with organizational security policies. Strong knowledge of cybersecurity protocols and incident response procedures is essential for effective threat management and minimizing risk exposure.
Perform security audits and compliance checks
Conduct thorough security audits to identify vulnerabilities and ensure adherence to industry standards and organizational policies. Evaluate systems and processes for compliance with regulatory requirements such as GDPR, HIPAA, or ISO 27001. Recommend actionable improvements to enhance overall security posture and maintain continuous compliance.
Develop cybersecurity policies and procedures
Create and implement cybersecurity policies and procedures that protect organizational data and ensure compliance with industry standards such as NIST and ISO 27001. Regularly update security protocols to address emerging threats, incorporating risk assessments and employee training to foster a culture of security awareness. Collaborate with IT and legal teams to align policies with regulatory requirements and enhance incident response capabilities.
Respond to security breaches and incidents
Respond to security breaches and incidents by quickly assessing the situation, isolating affected systems, and implementing corrective measures to minimize damage and ensure business continuity. Collaborate with IT teams to analyze root causes, document findings, and enhance security protocols to prevent future occurrences. Maintain up-to-date knowledge of cybersecurity threats and response techniques to effectively safeguard organizational assets.
Encrypt sensitive defense data
Encrypting sensitive defense data requires expertise in advanced cryptographic algorithms and secure communication protocols to protect classified information from unauthorized access. Candidates should demonstrate proficiency with encryption tools such as AES, RSA, and quantum-resistant methods, ensuring compliance with government cybersecurity standards like NIST SP 800-175 and DISA STIGs. Strong attention to detail and experience in risk assessment enhance the ability to maintain the integrity and confidentiality of defense data encryption systems.
Educate staff on cybersecurity best practices
Train employees on recognizing phishing attacks, managing strong passwords, and safeguarding sensitive information to reduce security risks. Develop and deliver regular workshops and interactive sessions that reinforce cybersecurity best practices. Encourage a culture of vigilance by providing up-to-date guidelines aligned with industry standards and company policies.
Ensure secure configuration of defense systems
Ensure secure configuration of defense systems by implementing robust cybersecurity protocols and regularly updating system software to protect against vulnerabilities. Conduct comprehensive security audits and threat assessments to identify potential risks and enforce mitigation strategies. Collaborate with IT and security teams to maintain compliance with industry standards and government regulations.
