A Network Administrator in a defense company designs, implements, and maintains secure communication networks essential for protecting sensitive military data. They monitor network performance, troubleshoot issues, and enforce cybersecurity protocols to prevent unauthorized access and cyber threats. Their role ensures reliable and secure connectivity critical for defense operations and information integrity.
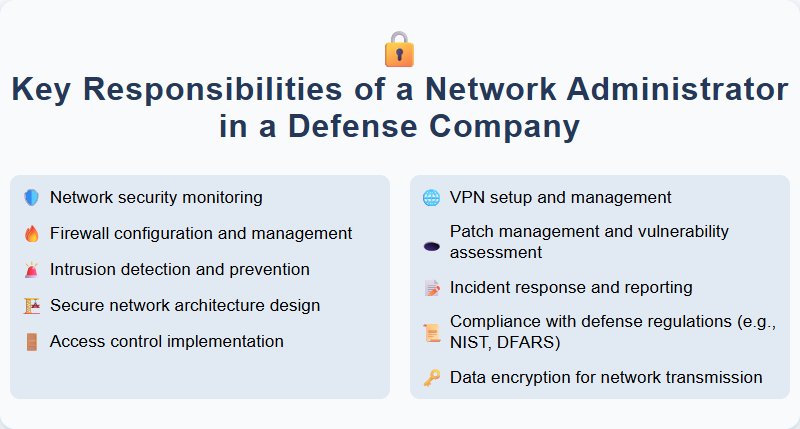
Network security monitoring
Network security monitoring involves continuous surveillance of an organization's digital infrastructure to detect and respond to potential threats in real-time. This role requires proficiency in using advanced intrusion detection systems (IDS), analyzing network traffic, and identifying vulnerabilities to prevent unauthorized access. Candidates should possess strong analytical skills, experience with security information and event management (SIEM) tools, and the ability to implement proactive measures to safeguard sensitive data.
Firewall configuration and management
Manage and optimize firewall configuration to ensure robust network security by implementing precise rules and policies that control inbound and outbound traffic. Monitor firewall performance regularly, conduct timely updates, and troubleshoot issues to maintain optimal protection against cyber threats. Collaborate with IT teams to align firewall settings with organizational security protocols and compliance requirements.
Intrusion detection and prevention
Experience in managing Intrusion Detection and Prevention Systems (IDPS) to monitor network traffic and identify potential security threats, vulnerabilities, and anomalies in real time. Skilled in analyzing alerts, tuning detection rules, and implementing remediation actions to prevent unauthorized access and ensure data integrity. Proactive in collaborating with cybersecurity teams to strengthen defense mechanisms and maintain compliance with industry security standards.
Secure network architecture design
Designing a secure network architecture involves creating a robust framework that protects data integrity and prevents unauthorized access by integrating firewalls, intrusion detection systems, and encryption protocols. Candidates should possess expertise in network security principles, risk assessment, and the implementation of multi-layered defense strategies to safeguard organizational assets. Proficiency in tools like VPNs, IDS/IPS, and knowledge of compliance standards such as ISO 27001 or NIST is essential for effective security architecture design.
Access control implementation
Implement and manage access control systems to safeguard sensitive areas and information by configuring hardware and software solutions. Conduct regular audits and update protocols to ensure compliance with security policies and industry standards. Collaborate with IT and security teams to identify vulnerabilities and recommend enhancements for robust access management.
VPN setup and management
Expertise in VPN setup and management includes configuring secure virtual private networks to ensure encrypted data transmission and remote access protection. Responsibilities encompass installation, monitoring, troubleshooting, and updating VPN protocols to maintain optimal network security and performance. Candidates should possess strong knowledge of IPsec, SSL/TLS, and multi-factor authentication integration to safeguard organizational resources.
Patch management and vulnerability assessment
Efficient patch management ensures that all software and systems are up-to-date, reducing security risks and improving operational stability. Regular vulnerability assessments identify potential threats and weaknesses, allowing for timely remediation and enhanced cybersecurity posture. Candidates should have experience with automated tools, risk prioritization, and compliance standards to effectively manage and mitigate vulnerabilities.
Incident response and reporting
Incident response and reporting involves promptly identifying, managing, and documenting security breaches or IT incidents to minimize damage and restore normal operations. Key responsibilities include analyzing threat patterns, coordinating with cross-functional teams, and maintaining detailed incident reports to support compliance and continuous improvement. Strong skills in cybersecurity protocols, communication, and analytical problem-solving are essential for effective incident management.
Compliance with defense regulations (e.g., NIST, DFARS)
Ensure strict adherence to defense regulations such as NIST and DFARS by implementing and maintaining robust compliance programs. Regularly conduct audits, risk assessments, and employee training to uphold regulatory standards and mitigate potential vulnerabilities. Collaborate with cross-functional teams to integrate compliance requirements into all defense-related processes and documentation.
Data encryption for network transmission
Implementing data encryption for network transmission involves securing sensitive information by converting it into unreadable code during transfer to prevent unauthorized access. This role requires expertise in encryption protocols such as AES, RSA, and TLS, ensuring data integrity and confidentiality across various communication channels. Candidates should be proficient in identifying potential vulnerabilities and deploying robust cryptographic solutions to enhance network security.
