A Data Center Administrator for a telecommunications company manages and maintains the infrastructure that supports network operations, ensuring optimal performance and uptime. They monitor servers, configure hardware, and implement security protocols to safeguard sensitive data and communication systems. Their role is critical in maintaining seamless connectivity and managing the data flow essential for telecom services.
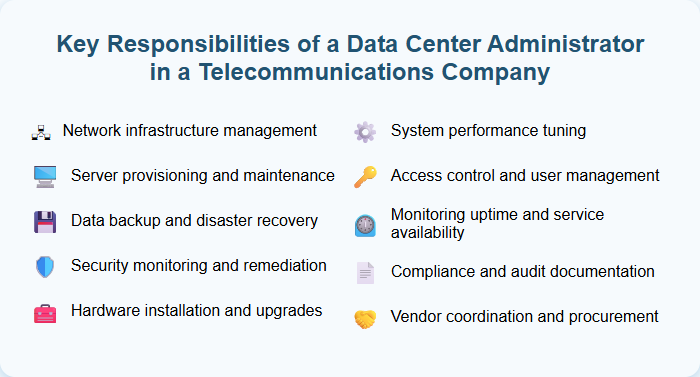
Network infrastructure management
Network infrastructure management involves overseeing the design, implementation, and maintenance of an organization's network systems to ensure optimal performance and security. Responsibilities include configuring routers, switches, firewalls, monitoring network traffic, and troubleshooting connectivity issues to minimize downtime. Professionals should possess expertise in network protocols, cybersecurity principles, and cloud integration to support scalable and resilient infrastructure.
Server provisioning and maintenance
Server provisioning and maintenance involves configuring and deploying servers to ensure optimal performance, security, and scalability. Tasks include installing operating systems, managing hardware resources, applying software updates, and monitoring system health to prevent downtime. Proficiency with automation tools like Ansible or Terraform and strong knowledge of network protocols can significantly enhance efficiency in server provisioning and ongoing maintenance.
Data backup and disaster recovery
Data backup and disaster recovery involve creating and maintaining reliable data backup systems to ensure business continuity during data loss or system failures. Responsibilities include designing backup strategies, performing regular backup verification, and developing comprehensive disaster recovery plans to minimize downtime. Candidates should have expertise in cloud storage solutions, data replication, and recovery testing to safeguard critical business information effectively.
Security monitoring and remediation
Security monitoring and remediation involves continuous surveillance of network traffic, systems, and applications to detect vulnerabilities, threats, and unauthorized activities in real time. Effective security monitoring tools and protocols enable swift identification and response to incidents, minimizing potential damage and ensuring compliance with industry standards. Regular remediation actions, such as patch management, configuration adjustments, and threat mitigation, are essential to maintain a robust security posture and safeguard organizational assets.
Hardware installation and upgrades
Perform comprehensive hardware installation and upgrades to ensure optimal system performance, including deploying new components, replacing outdated parts, and configuring devices for seamless integration. Troubleshoot hardware issues proactively to minimize downtime and enhance user experience by maintaining up-to-date technology standards. Collaborate with IT teams to evaluate system requirements and recommend best practices for efficient hardware lifecycle management.
System performance tuning
System performance tuning involves analyzing and optimizing hardware and software configurations to enhance overall efficiency and responsiveness. This process includes monitoring key metrics such as CPU usage, memory consumption, and disk I/O to identify bottlenecks or system limitations. Expertise in system performance tuning tools and techniques is essential to recommend and implement effective improvements for sustained operational excellence.
Access control and user management
Managing access control and user management involves overseeing the assignment of user permissions, ensuring secure authentication processes, and maintaining compliance with organizational security policies. This role requires continuous monitoring of user activity to prevent unauthorized access and managing roles to align with evolving business requirements. Candidates should be proficient in identity management systems and stay updated on best practices to protect sensitive data effectively.
Monitoring uptime and service availability
Monitor uptime and service availability by utilizing advanced network monitoring tools to ensure continuous operation and minimize downtime. Analyze performance metrics and promptly address incidents to maintain high system reliability and user satisfaction. Collaborate with IT teams to implement proactive maintenance and optimize service infrastructure for maximum efficiency.
Compliance and audit documentation
Ensure accurate and thorough maintenance of compliance and audit documentation to meet regulatory standards and internal policies. Regularly review and update records to support audit readiness and mitigate risk exposure. Implement systematic processes for documentation control to enhance transparency and accountability across departments.
Vendor coordination and procurement
Vendor coordination involves managing relationships with suppliers to ensure timely delivery and quality compliance, while procurement focuses on acquiring goods and services at optimal costs. Strong negotiation skills and a thorough understanding of supply chain processes enable efficient inventory management and cost savings. Proficiency in vendor evaluation and contract management strengthens the vendor coordination and procurement function, driving seamless operations and organizational success.
